Cross-border cloud compliance is about managing data across countries while adhering to regulations like GDPR, PIPL, and others. Non-compliance can lead to steep penalties, operational disruptions, and reputational damage. For example, Meta Ireland faced a €1.2 billion fine in 2023 for improper data transfers. Here's how to stay compliant:
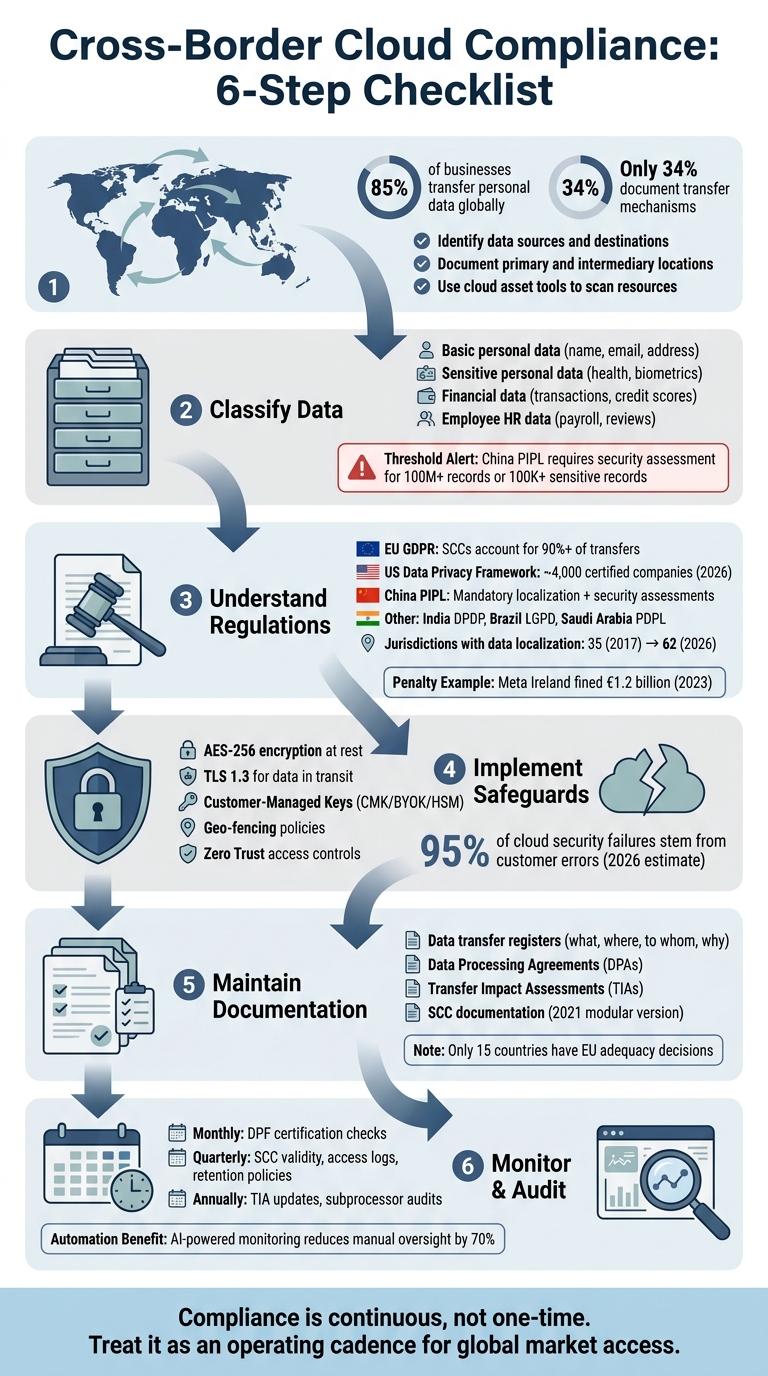
- Map Data Flows: Identify where data is stored and transferred. Only 34% of businesses document transfer mechanisms despite 85% transferring personal data globally.
- Classify Data: Categorize data (e.g., personal, sensitive, financial) and apply safeguards like encryption and access controls.
- Understand Regulations: Laws like GDPR, PIPL, and others require specific measures for data transfers. Use tools like Standard Contractual Clauses (SCCs) and Transfer Impact Assessments (TIAs).
- Implement Safeguards: Encrypt data, enforce geo-fencing, and use access controls to ensure compliance.
- Maintain Documentation: Keep detailed records of transfers, DPAs, and TIAs. Update them regularly.
- Monitor and Audit: Conduct regular audits, monitor vendor compliance, and automate breach detection.
6-Step Cross-Border Cloud Compliance Checklist
Cross-Border Data Transfer Regulations and Compliance Requirements | Exclusive Lesson
sbb-itb-17e8ec9
Map Your Data Flows and Classify Data
Understanding what data you have, where it’s stored, and how it moves is critical. Despite this, 85% of global businesses transfer personal data across borders, yet only 34% have documented transfer mechanisms.
Identify Data Sources and Destinations
Start by clearly outlining system boundaries. Avoid vague terms and instead name specific systems, integrations, and subprocessors. Your documentation should detail the primary destination (where data is ultimately stored), intermediary locations (like edge nodes), and the entire chain of subprocessors involved in handling the data.
Don’t overlook scenarios where data is accessed remotely, such as an employee in Germany working with a U.S.-based server. Use cloud asset tools to scan for resources containing data, including storage buckets, datasets, and SQL instances. To streamline policy enforcement and maintain geographic boundaries, organize cloud projects into region-specific folders like "EU Data" or "APAC Data".
"Cross-Border Data Transfers (US, EU, UK): Compliance Guide for 2026 is best executed as an operating cadence, not a one-time project." - Sebastien Ruosch, Executive Audit Director, Auditsuisse
Once you’ve identified your data sources and destinations, the next step is to classify the data based on its sensitivity to meet the appropriate regulatory requirements.
Categorize Data by Sensitivity
Classify your data into categories such as: basic personal data (e.g., name, email, address); sensitive personal data (e.g., health records, biometrics); financial data (e.g., transaction histories, credit scores); and employee HR data (e.g., payroll details, performance reviews). Each type of data has specific regulatory obligations. For instance, under China’s PIPL, organizations handling 100 million or more personal data records or 100,000 or more sensitive personal data records must conduct a security assessment.
Leverage resource labels in your cloud environment - like data_classification: "sensitive" - to automate policy enforcement and apply location constraints. Tools like Data Loss Prevention (DLP) can help mask sensitive details, such as email addresses, and strip location data before it crosses borders.
Once data is classified, mapping its flow is essential for maintaining control.
Document Your Data Flow
Create visual diagrams that trace data from its origin to its final destination, including all intermediary steps. Maintain an up-to-date spreadsheet that includes classification tags, sensitivity levels, and destination countries along with their relevant regulations. Assign responsibility for controls to roles rather than individuals - like "DevOps Lead" instead of "John Smith" - to ensure continuity even when team members change.
Regularly check whether your data volumes are nearing regulatory thresholds, as this may require mandatory assessments.
Understand Legal and Regulatory Requirements
After mapping your data flows, the next step is understanding the laws that govern your transfers. The regulatory landscape is shifting fast. For instance, jurisdictions with data localization requirements increased from 35 in 2017 to 62 in 2026. Between 2023 and 2026, nine jurisdictions tightened their rules, moving from conditional to strict requirements, with no signs of relaxing. It's essential to identify which laws apply to your operations to ensure compliance with both local and international mandates.
Key Regulations to Consider
The EU GDPR remains a benchmark regulation. It restricts data transfers to non-EEA countries unless there’s an adequacy decision or safeguards like Standard Contractual Clauses (SCCs) in place. SCCs account for more than 90% of these transfers. For EU-to-US transfers, the US Data Privacy Framework (DPF) provides an alternative, certification-based route. As of 2026, around 4,000 US companies - including major players like Microsoft, Google, Amazon, and Meta - are DPF-certified. Before transferring data, always verify the recipient's certification status on dataprivacyframework.gov.
China’s Personal Information Protection Law (PIPL) enforces stricter rules, requiring data localization and a government security assessment for companies processing 100 million or more personal data records or 100,000 sensitive records. In 2024, the Cyberspace Administration of China (CAC) imposed a fine of CNY 5 million on a tech firm for transferring over 500,000 records without completing the required security assessment.
Other regional laws also have varying requirements:
- India’s DPDP Act: Ranges from conditional to strict rules.
- Brazil’s LGPD: Requires safeguards similar to the GDPR.
- Saudi Arabia’s PDPL: Mandates localization for specific data types like health and financial records.
Failure to comply can result in severe penalties. For instance, in May 2023, Meta Ireland was fined EUR 1.2 billion by the Irish Data Protection Commission for unlawful EU–US transfers using SCCs without adequate supplementary measures to mitigate US surveillance risks.
Perform Transfer Impact Assessments (TIAs)
To ensure compliance with these regulations, Transfer Impact Assessments (TIAs) are crucial. They validate whether contractual safeguards like SCCs effectively mitigate risks tied to local laws. Post-Schrems II, TIAs are mandatory when relying on SCCs.
A TIA evaluates the legal environment of the destination country - such as surveillance laws like FISA 702 or the CLOUD Act in the US - and assesses how these might affect the protections in place.
"SCCs alone are insufficient: The TIA requirement mandates assessment of destination country legal environments." - AgentScout
Your TIA should include:
- A review of the destination country’s legal framework (e.g., surveillance laws and judicial oversight).
- Details of the transfer scenario, including data types, subprocessors, and encryption measures.
- Selection of supplementary measures based on risk (e.g., end-to-end encryption for high-risk data or pseudonymization for medium risk).
- A documented risk determination supported by evidence.
Additionally, maintain a centralized TIA register and conduct annual reviews to reflect changes in local laws.
Use Cloud Provider Compliance Tools
Cloud providers offer tools to simplify compliance efforts. For example, AWS Artifact provides on-demand access to compliance reports, certifications, and SOC reports that demonstrate adherence to global standards. Transparency reports, like Amazon Information Request Reports, help you monitor government data requests.
Leverage automated tools like Amazon Macie or Google Cloud DLP to identify and classify sensitive data (e.g., PII, PHI) before it crosses borders. Implement geo-fencing policies to ensure data remains stored in compliant regions. Also, update any outdated contracts - replace 2010 SCCs with the modular SCCs introduced in 2021 (Modules 1–4). These tools should be part of your regular compliance checklist to stay ahead in managing data transfers effectively.
Implement Technical Safeguards for Data Security
Meeting regulatory requirements isn't just about knowing the rules - it's about putting precise technical measures in place. While understanding the law is important, the real test is ensuring compliance as your team works across various cloud environments. By 2026, experts estimate that 95% of cloud security failures will stem from customer errors, not provider issues. This means your organization must take charge of configurations like encryption, access policies, and monitoring.
Encrypt Data at Rest and in Transit
Encryption is a cornerstone of data security. For data at rest, enable AES-256 encryption on all cloud storage and databases. Most major cloud providers already support this feature. For data in transit, use TLS 1.3 for transfers and enforce HTTPS on all public endpoints. When dealing with APIs, ensure you're using at least TLS 1.2+.
Key management plays a vital role here. Options like Customer-Managed Keys (CMK), Bring Your Own Key (BYOK), or Hardware Security Modules (HSM) give you full control over cryptographic keys. Request proof of key separation from your cloud providers to ensure they can't decrypt your data without explicit authorization. For compliance with local regulations, such as those in the EU, ensure encryption keys remain within the required jurisdiction. To verify data integrity during transfers, use SHA-256 checksums and store both pre- and post-transfer hashes in immutable logs.
Once encryption is in place, the focus turns to controlling access and movement of data.
Enforce Access Controls and Geo-Fencing
Strong access controls are critical to prevent unauthorized data movement. Use Service Control Policies (SCPs) through AWS Organizations or Azure Policy to block resource creation - like S3 buckets or virtual machines - in unauthorized regions. In Google Cloud, VPC Service Controls can establish perimeters to restrict data transfers between regional projects unless explicitly approved and audited.
Leverage Attribute-Based Access Control (ABAC) by tagging datasets with attributes like jurisdiction=EU and configuring key management policies to deny decryption requests from unapproved regions. Adopting a Zero Trust model, which includes workload identity federation and short-lived tokens, further strengthens security. On the network side, tools like Route 53 Resolver endpoints or specialized firewalls can restrict DNS resolution and control traffic to approved regional IPs.
Use AI-Powered Monitoring for Data Residency
Encryption and access controls are only part of the equation - continuous monitoring ensures compliance with data residency requirements. AI Gateways can act as a control layer between your applications and external model providers, ensuring data doesn’t cross regional boundaries during operations like inference or retries. These gateways, combined with automated policies, can monitor data residency in real time, flag risks instantly, and reduce the need for manual oversight by 70%. For industries like financial services, where regulatory alerts are frequent, platforms equipped with natural language processing (NLP) can interpret global regulations in multiple languages and provide timely updates.
To further safeguard data integrity, automate checks using SHA-256 hashing during migration windows to detect corruption or unauthorized changes. Additionally, set up automated 90-day key rotations with compliance gates to ensure cryptographic materials remain within the required jurisdiction.
Establish Documentation and Vendor Agreements
Technical safeguards are essential for protecting your data, but they’re only part of the equation. Detailed documentation and solid vendor agreements create the audit trail regulators expect. Under GDPR, unauthorized transfers can lead to fines as high as EUR 20 million or 4% of global annual turnover. Past penalties underscore why thorough records and vendor agreements are critical for compliance. Here’s how you can stay on top of both.
Maintain Data Transfer Registers
Having technical controls in place is a good start, but a strong documentation trail is equally important. A data transfer register acts as a logbook for every cross-border data movement, capturing the "what, where, to whom, and why." This register should include:
- Categories of data being transferred (e.g., customer PII, HR records, or health data)
- Destination countries
- Transfer mechanisms used, such as Standard Contractual Clauses (SCCs), Adequacy Decisions, Binding Corporate Rules, or the EU–US Data Privacy Framework
- Results of Transfer Impact Assessments (TIAs) for transfers to non-adequate countries
It’s also crucial to document supplementary measures like encryption with customer-controlled keys or pseudonymization to mitigate risks identified in TIAs. Your records need to be complete, up-to-date, and well-documented, with clear approval trails and notes for exceptions.
Keep in mind, only 15 countries are currently recognized by the EU as having "adequate" data protection laws. For transfers to other countries, additional legal measures are required. To simplify compliance, consider setting up log sinks in your cloud environment to automatically capture details of all cross-region data transfers, including the actor, operation, source location, and destination project.
Negotiate Data Processing Agreements (DPAs)
A well-crafted Data Processing Addendum (DPA) is more than just a legal formality - it’s a tool for ensuring compliance. For EU data transfers, use the modular SCCs introduced in 2021, choosing the appropriate module based on your relationship with the vendor (e.g., Controller-to-Controller or Processor-to-Processor). If you’re relying on an adequacy decision, such as the EU–US Data Privacy Framework, verify the vendor’s certification on the official website. Without certification, you’ll need to implement SCCs along with a TIA. Notably, by 2026, around 4,000 US companies, including Microsoft, Google, Amazon, and Meta, are expected to hold DPF certification.
Your DPA should also specify:
- Technical requirements like AES-256 encryption, customer-managed keys, and designated data residency regions
- Audit rights, allowing you to inspect the vendor’s infrastructure annually and requiring breach notifications within 24 hours
- Sub-processor controls, ensuring vendors get written authorization before engaging additional processors (per Clause 9 of the EU SCCs)
- A docking clause (Clause 7) to allow new subsidiaries or parties to join the agreement as your business grows
Avoid generic language in the annexes. Instead, detail specific processing activities and technical measures to ensure clarity and enforceability.
Monitor Vendor Compliance
Signing a DPA is just the start - ongoing monitoring is essential. Regularly check that transfer mechanisms remain valid. For example, verify quarterly that US vendors maintain active DPF certification on dataprivacyframework.gov. Update your TIAs annually to reflect any changes in the legal or surveillance landscape of destination countries. Additionally, conduct yearly audits of your vendors’ sub-processor chains to confirm compliance.
"A UK healthcare provider was fined GBP 200,000 by the Information Commissioner's Office for transferring patient data to the US without implementing SCCs or conducting a required TIA."
Similarly, a French e-commerce company was fined EUR 150,000 by the CNIL for transferring employee data to China without completing provincial CAC filings.
To streamline compliance, use a centralized dashboard to track SCCs, DPF certifications, filing deadlines, and TIA updates in real time. Cloud tools like VPC Service Controls can also prevent unauthorized data movement between regional projects. Finally, retain signed DPAs for the duration of the processing period plus the applicable statute of limitations - usually 3 to 6 years.
Regularly Audit, Monitor, and Update Compliance Measures
Compliance isn’t a one-and-done task - it’s an ongoing commitment. Regulations, risks, and infrastructure evolve constantly, meaning your compliance measures need to keep pace. To maintain a strong compliance framework, regular audits, automated monitoring, and consistent updates are essential.
Conduct Periodic Audits and Penetration Tests
Frequent security assessments are key to identifying vulnerabilities before regulators or bad actors do. Start with quarterly reviews to confirm that your Standard Contractual Clauses (SCCs) and Data Privacy Framework (DPF) certifications are still valid. For U.S. vendors, you can verify active certifications at dataprivacyframework.gov. These reviews should also include audits of access logs and retention policies. Annual audits should go deeper, updating Transfer Impact Assessments (TIAs) in line with changes to surveillance laws in destination countries, auditing subprocessors to ensure they comply with Data Processing Agreements, and conducting unannounced remote attestations for trusted execution environments like Intel TDX or AMD SEV for workloads with high sensitivity.
Additionally, hold monthly control reviews with your engineering, security, and compliance teams to catch deviations from documented policies. Internal walkthroughs before audits help verify timestamps, ensure reviewer independence, and confirm that policies are being implemented as intended. Auditors will expect evidence that is accurate, timely, and reproducible.
Here’s a quick reference table to streamline your compliance checks:
| Monitoring Activity | Frequency | Responsible Party |
|---|---|---|
| Transfer mechanism validity check | Quarterly | DPO / Compliance Team |
| TIA review and update | Annually | Legal Counsel |
| Subprocessor audit | Annually | Compliance Team |
| DPF certification status check | Monthly | IT Security |
| Access log & retention audit | Quarterly | IT / Compliance |
Automate Breach Detection and Regulatory Updates
Once your audits are in place, automation tools can help you scale monitoring efforts as your organization grows. AI-powered tools can detect, diagnose, and even resolve security incidents through root cause analysis and automated code fixes. For near real-time monitoring of cross-border data flows, integrate cloud provider logs with a Security Information and Event Management (SIEM) system.
Platforms like OneTrust and TrustArc simplify the creation and management of SCCs and TIAs. These tools can also map internal retention policies to local regulations, ensuring data is archived or deleted in compliance with shifting jurisdictional laws. BigID is another useful tool for organizations handling large data volumes, offering automated discovery and detection of sensitive data across your infrastructure.
Set up automated triggers to review TIAs whenever a destination country’s laws change or when you onboard a new subprocessor. Use machine-readable compliance manifests to streamline the vetting of third-party vendors and verify their data residency status. If you operate in China, keep a close eye on data volumes - processing over 100 million personal data records triggers a mandatory security review by the Cyberspace Administration of China (CAC).
Schedule Regular Compliance Reviews
A structured evidence calendar can help you stay organized and avoid last-minute panic before audits. Monthly, quarterly, and annual reviews should align with the frequency of your controls. For example, quarterly reviews should incorporate lessons learned into broader governance frameworks and validate transfer mechanisms. Annual reviews should include TIA updates, subprocessor audits, and checks on China filing statuses.
"Teams that treat compliance as a sales-aligned operating function outperform teams that treat audits as episodic projects." – Sebastien Ruosch, Executive Audit Director, Auditsuisse
Be proactive about compliance checks. Trigger reviews whenever laws change in a receiving country or when new data flows are identified. For operations in China, remember that security assessments are typically valid for two years and require renewal after that period. U.S. companies using the Data Privacy Framework must also complete an annual self-certification renewal to stay on the active list. Finally, assign control ownership to specific roles rather than individuals to ensure continuity, even when staff transitions occur.
Conclusion
Cross-border cloud compliance isn't a one-and-done task - it’s a continuous process. By mapping data flows, adhering to legal standards, implementing technical safeguards, and keeping detailed records, companies can build trust with customers, partners, and regulators alike. Startups that view compliance as an opportunity rather than a hurdle can open doors to global markets, lower the risk of incidents, and drive growth.
This perspective is echoed by industry experts:
"Regulation is no longer just a liability to manage; when approached as a productized capability, it strengthens trust with customers, reduces incident risk, and accelerates market access." – Alex Morgan, Senior Editor & Cloud Security Strategist, Smartcyber.cloud
Leveraging AI-driven tools for automation can transform compliance efforts. Instead of scrambling for reactive audits, teams can shift to continuous monitoring, cutting audit prep time from months to days. By embedding policies directly into infrastructure with policy-as-code engines and automated evidence pipelines, compliance becomes both mandatory and scalable.
For startups juggling compliance and financial operations, integrating these processes can further enhance their competitive edge. Tools like Lucid Financials offer AI-powered bookkeeping, real-time Slack support, and investor-ready reporting. This kind of intelligent automation allows teams to prioritize growth while maintaining strong data governance and financial transparency.
FAQs
Which of our data transfers actually count as “cross-border”?
Cross-border data transfers happen when personal data is moved between countries - say, from the US to the EU or China. This often involves transferring the data for purposes like processing or storage. Such transfers must align with international data laws to ensure compliance.
When do we need SCCs, a TIA, or the EU–US Data Privacy Framework?
When transferring data from the EU to non-EU countries without an adequacy decision in place, Standard Contractual Clauses (SCCs) are essential. To assess the risks associated with these mechanisms (or alternatives like the EU–US Data Privacy Framework), a Transfer Impact Assessment (TIA) is conducted. The EU–US Data Privacy Framework can serve as an alternative transfer mechanism, provided it meets adequacy requirements. It's crucial to ensure compliance with all relevant regulations governing cross-border data transfers.
What’s the fastest way to enforce data residency in AWS, Azure, or Google Cloud?
The quickest way to ensure data residency in AWS, Azure, or Google Cloud is by setting up region-specific policies and controls to limit where data can be stored and transferred.
- AWS: Use IAM policies to restrict the regions where S3 buckets can be created or accessed.
- Google Cloud: Apply organization policies to prevent resource creation outside designated regions.
- Azure: Leverage Azure Policy to enforce rules on deployment locations.
To maintain compliance, implement continuous monitoring to track and address any deviations.


